TorZon Market — Definitive Security & OPSEC Playbook
This isn't a gentle introduction. If you're here, you already know why OPSEC matters — or you've learned the hard way. This playbook covers everything from basic operational security hygiene to advanced threat identification. We've written it based on real incidents, real scams, and real losses that could have been prevented. Read it. Bookmark it. Actually follow it.

TorZon Market Tor — Pre-Access Security Checklist
Before you even open Tor Browser, go through this list. Every. Single. Time.
- Use a dedicated device or VM for darknet access — not your daily driver
- Ensure your OS is fully patched and up to date
- Disable location services, Bluetooth, and unnecessary background services
- Use a VPN before connecting to Tor (Tor → VPN → Internet) if your threat model requires it
- Verify Tor Browser download via GPG signature
- Use a clean, separate email address (ProtonMail or similar) for any market accounts
- Never use the same password across any two services — ever
- Enable 2FA on your TorZon account and your email
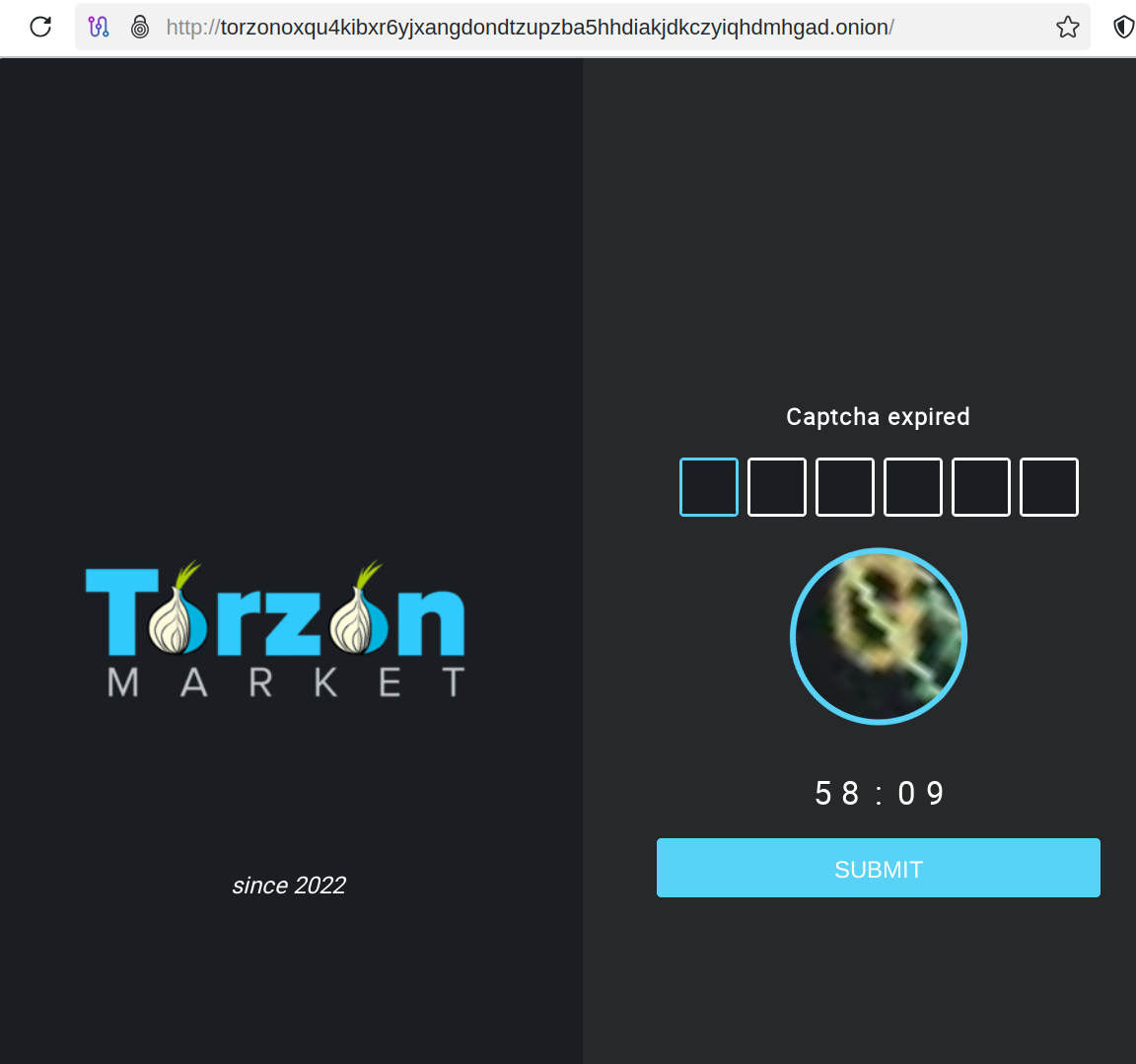
TorZon Market Darknet — Phishing Red Flags
We've catalogued the most common phishing tactics targeting TorZon users. This isn't theoretical — these are techniques we've seen deployed in the wild, some as recently as last week.
| Red Flag | What It Looks Like | How to Verify |
|---|---|---|
| URL mismatch | One or two characters different from the real .onion | Compare character-by-character with the URL on this page |
| Missing captcha | Login page loads directly without captcha challenge | Real TorZon always shows captcha before login |
| Fast load times | Page loads in under 1 second on Tor | Legitimate onion sites take 2–5 seconds minimum |
| Unusual login fields | Asks for recovery phrase, seed words, or PIN at login | TorZon only asks username + password + 2FA |
| PGP key mismatch | Signed messages don't verify against known public key | Import the known key and verify every time |
| Unsolicited link | Someone DMs you a "new" or "faster" mirror | Never use links from DMs. Period. |
How to Access TorZon — OPSEC Best Practices
Network Security
Your network is the first thing to secure. If your ISP can see you're connecting to Tor, that's already more information than they should have. Consider using bridges (obfs4 or meek-azure) to disguise Tor traffic. If you're on a network you don't control (workplace, hotel, café), assume everything is logged.
Device Security
Full disk encryption is non-negotiable. On Linux, use LUKS. On Windows, BitLocker. On macOS, FileVault. If your device is seized, encryption is the only thing between your data and whoever has it. Also: disable USB autorun, disable remote management, and keep your firewall active.
Account Security
Your TorZon account is only as secure as its weakest link. That usually means your password. Use a password manager (KeePassXC — offline, not cloud-based) and generate a random 20+ character password. Enable 2FA. Use a PGP key for all communications. Don't reuse any credentials.
TorZon Market Link — Evolving Scam Techniques
Scammers adapt. Here's what's been trending in early 2026:
Case Study 1: The "Official Support" DM
A user on Dread received a DM from an account claiming to be "TorZon Support" saying their account had been flagged and they needed to "re-verify" through a special link. The link led to a pixel-perfect phishing page. The user entered their credentials, and within 8 minutes, their balance was withdrawn. TorZon staff will never DM you. Support is only available through the market's built-in ticket system.
Case Study 2: The "Updated Mirror" Forum Post
A forum post (not on Dread) advertised a "faster mirror" for TorZon that was "closer to European servers." The link was a phishing clone with a near-identical URL. Dozens of users reported losses before the post was taken down. Official mirrors are only listed on verified pages like this one.
Case Study 3: The Man-in-the-Middle Clipboard Attack
Malware on a user's system replaced .onion URLs in the clipboard with a phishing URL. The user copied the correct URL but a different one was pasted into Tor Browser. This is why you should visually verify the address bar after pasting — every time, no exceptions.
TorZon Market Onion — Security FAQ
Q: Do I really need a VPN with Tor?
It depends on your threat model. A VPN prevents your ISP from seeing Tor traffic, but it means your VPN provider can. If you trust your VPN more than your ISP, use one. If not, bridges may be sufficient. There's no universal right answer.
Q: Is Tails better than Whonix?
Different tools for different needs. Tails is amnesic — it forgets everything after shutdown. Whonix provides persistent isolation via two VMs. For one-time access, Tails. For ongoing use with saved settings, Whonix. Both are vastly better than bare-metal Tor Browser.
Q: What's the biggest OPSEC mistake people make?
Password reuse. Hands down. Second place is trusting links from Telegram channels. Third is logging in from their daily-driver OS without any isolation.
Q: How do I verify TorZon's PGP key?
Import the key from at least two independent verified sources. Sign a test message to yourself to confirm. Then verify all market communications against it. If the key has changed and you haven't seen an official migration announcement — assume compromise.